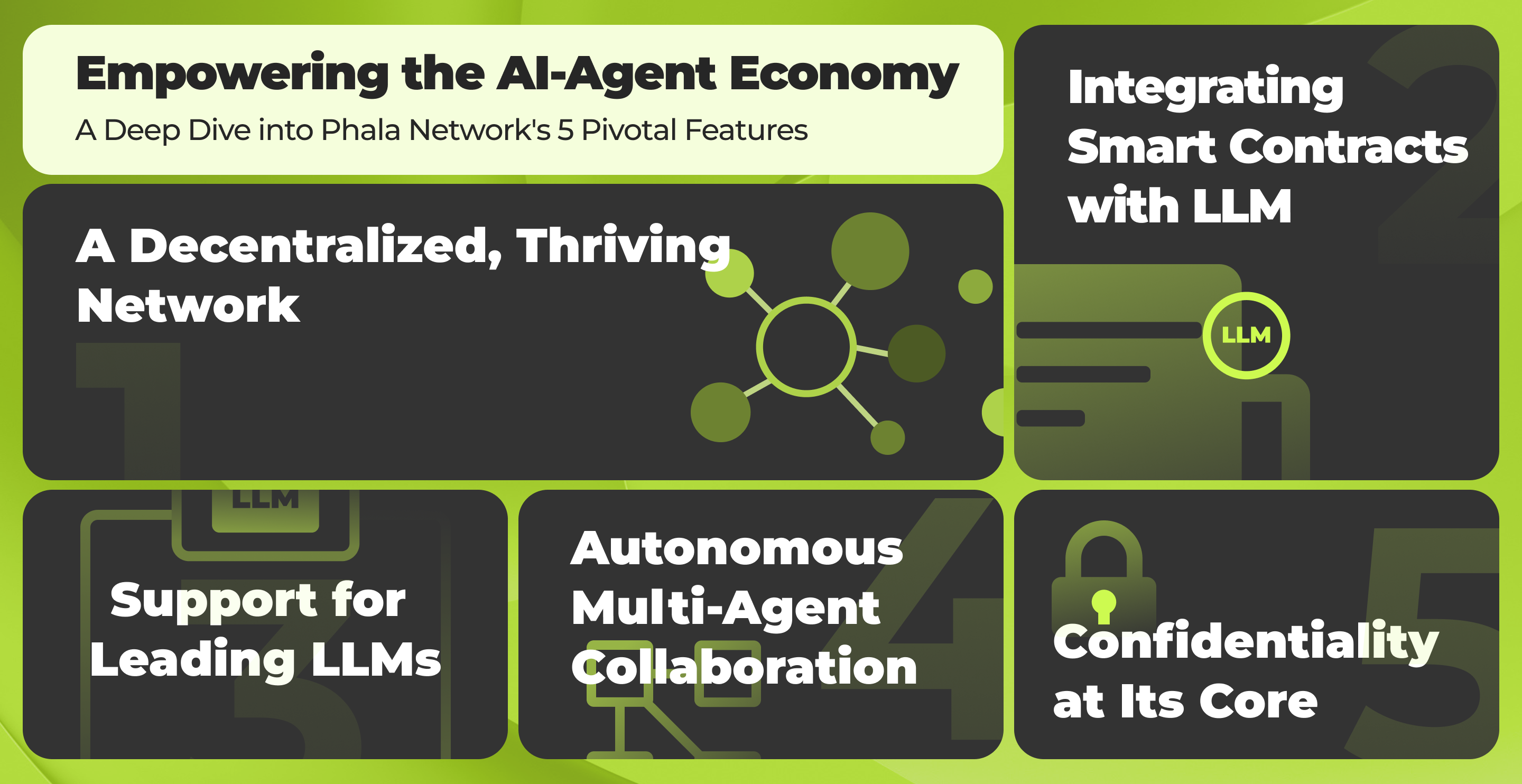
AI Coprocessor
for Blockchains
Easily Integrate AI & Web3
Read Data
Read Data
ChatGPT
Alchemy
Arweave
Binance
ChatGPT
Alchemy
Filecoin
Gmail
Arweave
Graph Protocol
ChatGPT
Binance
Uniswap
Filecoin
Polygon
Binance
Gmail
Uniswap
Graph Protocol
Gmail
Filecoin
Arweave
Push
ChatGPT
Filecoin
Arweave
ChatGPT
Alchemy
Push
Arweave
Uniswap
Graph Protocol
Binance
Uniswap
Gmail
Filecoin
Polygon
Alchemy
Binance
Push
Uniswap
Push
Uniswap
Filecoin
AWS cloud
Lens
Polygon
ChatGPT
Push
Binance
Graph Protocol
AWS cloud
Binance
Arweave
AWS cloud
Filecoin
Gmail
Uniswap
Arweave
Gmail
Alchemy
Uniswap
ChatGPT
Arweave
Push
Binance
ChatGPT
Push
Internet
Uniswap
Arweave
Ethereum
Graph Protocol
ChatGPT
Arweave
Uniswap
ChatGPT
Arweave
Filecoin
Arweave
Ethereum
Arweave
Uniswap
Gmail
Arweave
Uniswap
Alchemy
Push
Binance
Filecoin
Binance
ChatGPT
Analyze text with LLM
Alchemy
Traditional B lockchain data Access
Arweave
Permanent and Decentralized Storage
Binance
Traditional Finance
ChatGPT
Analyze text with LLM
Alchemy
Traditional B lockchain data Access
Filecoin
Decentralized Storage
Gmail
Email notification
Arweave
Permanent and Decentralized Storage
Graph Protocol
Decentralized Blockchain Data Access
Traditional Social Media
ChatGPT
Analyze text with LLM
Binance
Traditional Finance
Uniswap
Decentralized AMM
Filecoin
Decentralized Storage
Traditional Social Media
Polygon
Services and DApps on L1
Binance
Traditional Finance
Gmail
Email notification
Uniswap
Decentralized AMM
Graph Protocol
Decentralized Blockchain Data Access
Traditional Social Media
Gmail
Email notification
Filecoin
Decentralized Storage
Arweave
Permanent and Decentralized Storage
Traditional Social Media
Push
Decentralized Notification
ChatGPT
Analyze text with LLM
Filecoin
Decentralized Storage
Arweave
Permanent and Decentralized Storage
ChatGPT
Analyze text with LLM
Alchemy
Traditional B lockchain data Access
Push
Decentralized Notification
Arweave
Permanent and Decentralized Storage
Traditional Social Media
Uniswap
Decentralized AMM
Graph Protocol
Decentralized Blockchain Data Access
Binance
Traditional Finance
Uniswap
Decentralized AMM
Gmail
Email notification
Filecoin
Decentralized Storage
Polygon
Services and DApps on L1
Alchemy
Traditional B lockchain data Access
Binance
Traditional Finance
Push
Decentralized Notification
Uniswap
Decentralized AMM
Traditional Social Media
Push
Decentralized Notification
Uniswap
Decentralized AMM
Traditional Social Media
Filecoin
Decentralized Storage
AWS cloud
Traditional API and Database
Lens
Decentralized Web3 Social
Polygon
Services and DApps on L1
ChatGPT
Analyze text with LLM
Push
Decentralized Notification
Binance
Traditional Finance
Graph Protocol
Decentralized Blockchain Data Access
AWS cloud
Traditional API and Database
Binance
Traditional Finance
Arweave
Permanent and Decentralized Storage
AWS cloud
Traditional API and Database
Filecoin
Decentralized Storage
Gmail
Email notification
Uniswap
Decentralized AMM
Arweave
Permanent and Decentralized Storage
Gmail
Email notification
Alchemy
Traditional B lockchain data Access
Uniswap
Decentralized AMM
Traditional Social Media
ChatGPT
Analyze text with LLM
Arweave
Permanent and Decentralized Storage
Push
Decentralized Notification
Binance
Traditional Finance
ChatGPT
Analyze text with LLM
Push
Decentralized Notification
Internet
From Any HTTP API
Uniswap
Decentralized AMM
Arweave
Permanent and Decentralized Storage
Ethereum
Services and DApps on L1
Graph Protocol
Decentralized Blockchain Data Access
ChatGPT
Analyze text with LLM
Arweave
Permanent and Decentralized Storage
Uniswap
Decentralized AMM
ChatGPT
Analyze text with LLM
Arweave
Permanent and Decentralized Storage
Filecoin
Decentralized Storage
Traditional Social Media
Arweave
Permanent and Decentralized Storage
Ethereum
Services and DApps on L1
Traditional Social Media
Arweave
Permanent and Decentralized Storage
Uniswap
Decentralized AMM
Gmail
Email notification
Arweave
Permanent and Decentralized Storage
Uniswap
Decentralized AMM
Alchemy
Traditional B lockchain data Access
Traditional Social Media
Push
Decentralized Notification
Binance
Traditional Finance
Filecoin
Decentralized Storage
Traditional Social Media
Binance
Traditional Finance
Compute

Verify & Use
Filecoin
Gmail
Lens
Push
Polygon
Lens
Graph Protocol
Push
Lens
Graph Protocol
Binance
AWS cloud
Ethereum
Lens
Binance
Polygon
Ethereum
Uniswap
Lens
Ethereum
OP L2s
AWS cloud
Ethereum
OP L2s
Gmail
Alchemy
Blockchain
OP L2s
Polygon
Graph Protocol
AWS cloud
Filecoin
Alchemy
Push
ChatGPT
Ethereum
AWS cloud
Graph Protocol
Polygon
OP L2s
Alchemy
Ethereum
Push
Lens
OP L2s
Polygon
Gmail
Graph Protocol
Push
Ethereum
OP L2s
Polygon
Graph Protocol
Uniswap
Lens
Alchemy
Binance
AWS cloud
Gmail
Polygon
Lens
OP L2s
Gmail
Lens
Graph Protocol
AWS cloud
OP L2s
Filecoin
Graph Protocol
Polygon
Ethereum
AWS cloud
Graph Protocol
Alchemy
OP L2s
Binance
Lens
Filecoin
AWS cloud
Ethereum
Alchemy
Lens
OP L2s
Polygon
Ethereum
Lens
OP L2s
Polygon
Gmail
OP L2s
Ethereum
ChatGPT
AWS cloud
Ethereum
Alchemy
Push
Polygon
OP L2s
Alchemy
ChatGPT
OP L2s
Gmail
Filecoin
Decentralized Storage
Gmail
Email notification
Lens
Decentralized Web3 Social
Push
Decentralized Notification
Polygon
Services and DApps on L1
Lens
Decentralized Web3 Social
Graph Protocol
Decentralized Blockchain Data Access
Push
Decentralized Notification
Lens
Decentralized Web3 Social
Graph Protocol
Decentralized Blockchain Data Access
Binance
Traditional Finance
AWS cloud
Traditional API and Database
Ethereum
Services and DApps on L1
Lens
Decentralized Web3 Social
Binance
Traditional Finance
Polygon
Services and DApps on L1
Ethereum
Services and DApps on L1
Uniswap
Decentralized AMM
Lens
Decentralized Web3 Social
Ethereum
Services and DApps on L1
OP L2s
Services and DApps on L2
AWS cloud
Traditional API and Database
Ethereum
Services and DApps on L1
OP L2s
Services and DApps on L2
Gmail
Email notification
Alchemy
Traditional B lockchain data Access
Blockchain
To the Trustless World
OP L2s
Services and DApps on L2
Polygon
Services and DApps on L1
Graph Protocol
Decentralized Blockchain Data Access
AWS cloud
Traditional API and Database
Filecoin
Decentralized Storage
Alchemy
Traditional B lockchain data Access
Push
Decentralized Notification
ChatGPT
Analyze text with LLM
Ethereum
Services and DApps on L1
AWS cloud
Traditional API and Database
Graph Protocol
Decentralized Blockchain Data Access
Polygon
Services and DApps on L1
OP L2s
Services and DApps on L2
Alchemy
Traditional B lockchain data Access
Ethereum
Services and DApps on L1
Push
Decentralized Notification
Lens
Decentralized Web3 Social
OP L2s
Services and DApps on L2
Polygon
Services and DApps on L1
Gmail
Email notification
Graph Protocol
Decentralized Blockchain Data Access
Push
Decentralized Notification
Ethereum
Services and DApps on L1
OP L2s
Services and DApps on L2
Polygon
Services and DApps on L1
Graph Protocol
Decentralized Blockchain Data Access
Uniswap
Decentralized AMM
Lens
Decentralized Web3 Social
Alchemy
Traditional B lockchain data Access
Binance
Traditional Finance
AWS cloud
Traditional API and Database
Gmail
Email notification
Polygon
Services and DApps on L1
Lens
Decentralized Web3 Social
OP L2s
Services and DApps on L2
Gmail
Email notification
Lens
Decentralized Web3 Social
Graph Protocol
Decentralized Blockchain Data Access
AWS cloud
Traditional API and Database
OP L2s
Services and DApps on L2
Filecoin
Decentralized Storage
Graph Protocol
Decentralized Blockchain Data Access
Polygon
Services and DApps on L1
Ethereum
Services and DApps on L1
AWS cloud
Traditional API and Database
Graph Protocol
Decentralized Blockchain Data Access
Alchemy
Traditional B lockchain data Access
OP L2s
Services and DApps on L2
Binance
Traditional Finance
Lens
Decentralized Web3 Social
Filecoin
Decentralized Storage
Traditional Social Media
AWS cloud
Traditional API and Database
Ethereum
Services and DApps on L1
Alchemy
Traditional B lockchain data Access
Lens
Decentralized Web3 Social
OP L2s
Services and DApps on L2
Polygon
Services and DApps on L1
Ethereum
Services and DApps on L1
Lens
Decentralized Web3 Social
OP L2s
Services and DApps on L2
Polygon
Services and DApps on L1
Gmail
Email notification
OP L2s
Services and DApps on L2
Ethereum
Services and DApps on L1
ChatGPT
Analyze text with LLM
AWS cloud
Traditional API and Database
Ethereum
Services and DApps on L1
Alchemy
Traditional B lockchain data Access
Push
Decentralized Notification
Polygon
Services and DApps on L1
OP L2s
Services and DApps on L2
Alchemy
Traditional B lockchain data Access
ChatGPT
Analyze text with LLM
OP L2s
Services and DApps on L2
Gmail
Email notification
Verify & Use
AI-Agent Contract
Ship AI agents in minutes
Build with familiar tools
Backing 153 Contracts
Connect AI-Agent with 25+ Blockchains Instantly
Lens Protocol
Zurf
Huddle01
Sygma
KoinGaroo
inDEX
VRF Oracle
DMail
How It Works
Correctness
Phat Contracts are deployed to the blockchain and assigned to the offchain workers, running inside Secure Enclaves. Anyone can check the signed transactions and Secure Enclave remote attestation to verify that the executed code is the one published on the blockchain.
Replicated
Phat Contracts are deployed to one or more workers, grouped as a Cluster. The contracts in the same cluster are replicated to further guarantee the availability. Thanks to the redundancy by the Cluster design, the developer can further validate the states across the workers to...
Confidentiality
Phala Network implemented end-to-end encryption during the full Phat Contract lifecycle. Secure Enclave acts as a two-way sandbox that encrypts input, output, and internet access, protecting the secrets in the enclave against software and hardware level attack.
How Phala Network works
DePIN with the most TEE nodes
By the people, for the people
0
0
Recent Highlights